
Blockchain analytics investigators have uncovered an individual linked to a cryptocurrency laundering operation that is offering stolen tokens at discounted prices from recent high-profile exchange hacks.
Speaking exclusively to Cointelegraph, a representative from blockchain security firm Match Systems outlined how investigations into several major breaches featuring similar methods through the summer months of 2023 have pointed to an individual who is allegedly selling stolen cryptocurrency tokens via peer-to-peer transfers.
Related: CoinEx hack: Compromised private keys led to $70M theft
The investigators managed to identify and make contact with an individual on Telegram offering stolen assets. The team confirmed that the user was in control of an address containing over $6 million worth of cryptocurrencies after receiving a small transaction from the corresponding address.
The exchange of stolen assets was then conducted through a specially created Telegram bot, which offered a 3% discount off the token’s market price. Following initial conversations, the owner of the address reported that the initial assets on offer had been sold and that new tokens would be available some three weeks later:
“Maintaining our contact, this individual notified us about the commencement of new asset sales. Based on the available information, it is logical to assume that these are funds from CoinEx or Stake companies.”
The Match Systems team has not been able to fully identify the individual but has narrowed down their location to the European time zone based on several screenshots they had received and timings of conversations:
“We believe he is not part of the core team but is associated with them, possibly having been de-anonymized as a guarantee that he will not misuse the delegated assets.”
The individual also reportedly displayed “unstable” and “erratic” behavior during various interactions, abruptly leaving conversations with excuses like “Sorry, I must go; my mom is calling me to dinner”.
“Typically, he offers a 3% discount. Previously, when we first identified him, he would send 3.14 TRX as a form of proof to potential clients.”
Match Systems told Cointelegraph that the individual accepted Bitcoin (BTC) as a means of payment for the discounted stolen tokens and had previously sold $6 million worth of TRON (TRX) tokens. The latest offering from the Telegram user has listed $50 million worth of TRX, Ether (ETH) and Binance Smart Chain (BSC) tokens.
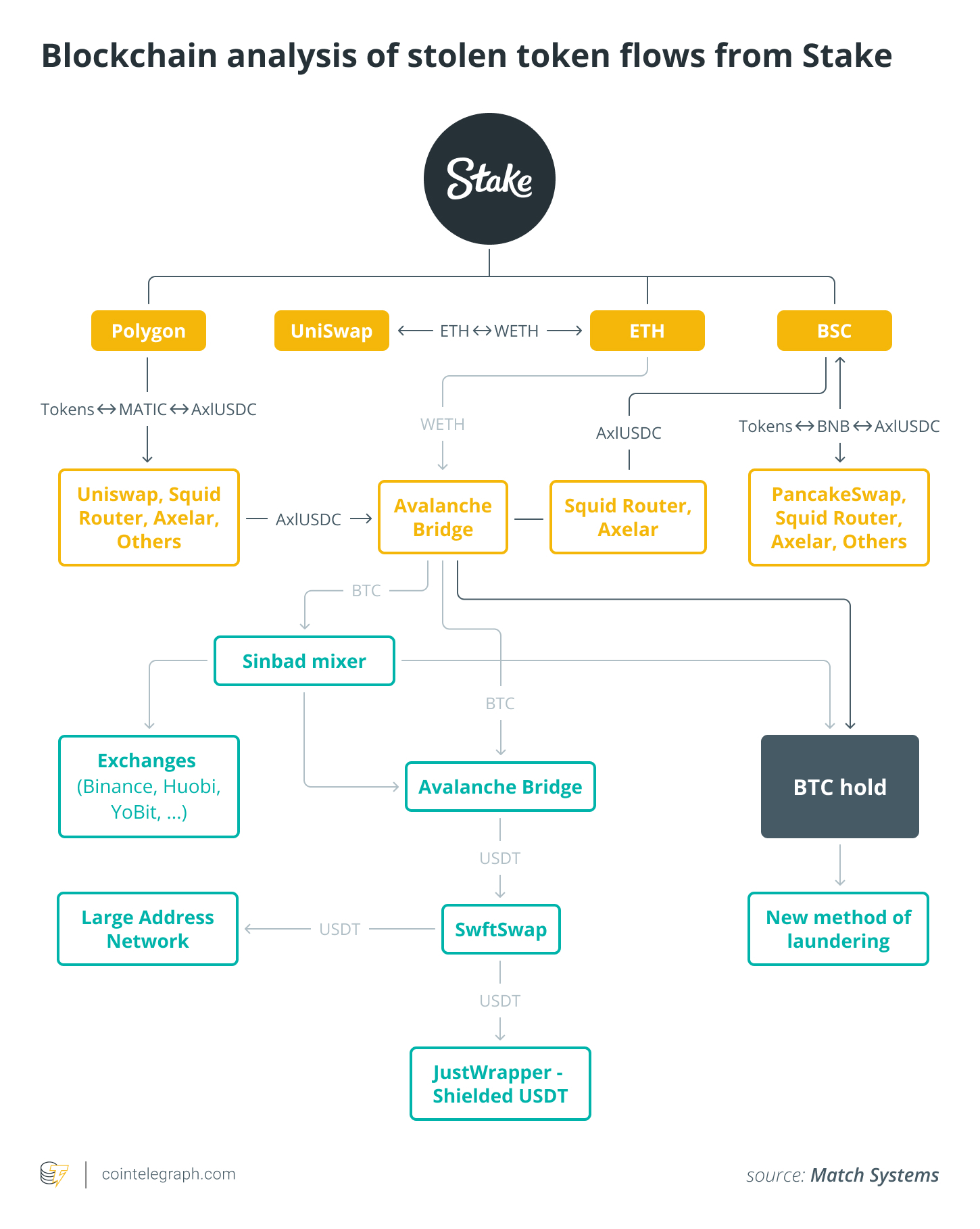
Blockchain security firm CertiK previously outlined the movement of stolen funds from the Stake heist in correspondence with Cointelegraph, with around $4.8 million of the total $41 million being laundered through various token movements and cross-chain swaps.
FBI later identified North Korean Lazarus Group hackers as the culprits of the Stake attack, while cyber security firm SlowMist also linked the $55 million CoinEx hack to the North Korean group.
This is in slight contrast to information obtained by Cointelegraph from Match Systems which suggests that the perpetrators of the CoinEx and Stake hacks had slightly different identifiers in methodology.
Their analysis highlights that previous Lazarus Group laundering efforts did not involve Commonwealth of Independent States (CIS) nations like Russia and Ukraine while the 2023 summer hacks saw stolen funds being actively laundered in these jurisdictions.
Related: Stake hack of $41M was performed by North Korean group: FBI
Lazarus hackers left minimal digital footprints behind while recent incidents have left plenty of breadcrumbs for investigators. Social engineering has also been identified as a key attack vector in the summer hacks while Lazarus Group targeted “mathematical vulnerabilities”.
Lastly the firm notes that Lazarus hackers typically used Tornado Cash to launder stolen cryptocurrency while recent incidents have seen funds mixed through protocols like Sinbad and Wasabi. Key similarities are still significant. All these hacks have used BTC wallets as the primary repository for stolen assets as well as the Avalanche Bridge and mixers for token laundering.
Blockchain data reviewed at the end of Sept. 2023 suggests that North Korean hackers have stolen an estimated $47 million worth of cryptocurrency this year, including $42.5 million in BTC and $1.9 million ETH.
Magazine: Blockchain detectives: Mt. Gox collapse saw birth of Chainalysis





Be the first to comment